
Huawei is the state run Chinese telecom infrastructure provider, who’s aggressive pricing and high quality devices have made them the favourite of many national IT backbones (including Britain). Are they involved with GhostNet and could they be used for further international espionage?
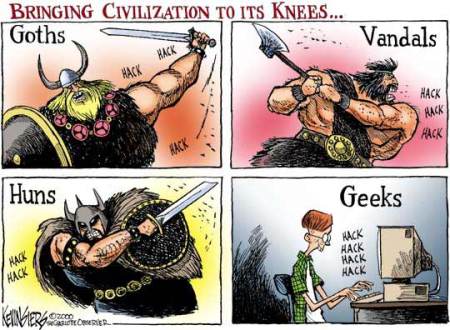
IT security threats and web wars are an integral component of today’s security and humanitarian landscape. Much has been made about Twitter’s role in the recent Iranian social unrest, for example. A recent Reuters report suggests that Isreal is turning to cyberwarfare for increasingly sophisticated jamming attacks and offensives.
“Asked to speculate about how Israel might target Iran, Borg said malware — a commonly used abbreviation for “malicious software” — could be inserted to corrupt, commandeer or crash the controls of sensitive sites like uranium enrichment plants.
Such attacks could be immediate, he said. Or they might be latent, with the malware loitering unseen and awaiting an external trigger, or pre-set to strike automatically when the infected facility reaches a more critical level of activity.”
Organised and swarm-based attacks on central state infrastructure has become so common as to barely warrant news mention. A North Korean bot net is currently attacked dozens of US government websites in Seoul (“North Korea Launches Massive Cyberattack on Seoul“) From Slashdot:
“A botnet composed of about 50,000 infected computers has been waging a war against US government Web sites and causing headaches for businesses in the US and South Korea. The attack started Saturday, and security experts have credited it with knocking the Federal Trade Commission’s (FTC’s) web site offline for parts of Monday and Tuesday. Several other government Web sites have also been targeted, including the Department of Transportation.”
GhostNet
Although these attacks are from North Korea, many others originate in China. A recent study from by the InfoWar Monitor uncovered a “massive Chinese espionage network,” called GhostNet. The Guardian reports:
“GhostNet appears to target embassies, media groups, NGOs, international organisations, government foreign ministries and the offices of the Dalai Lama.
After 10 months of study, the researchers concluded that GhostNet had invaded 1,295 computers in 103 countries, but it appeared to be most focused on countries in south Asia and south-east Asia, as well as the Dalai Lama’s offices in India, Brussels, London and New York. The network continues to infiltrate dozens of new computers each week.
There was a similar article in the New York Times, “Vast Spy System Loots Computers in 103 Countries“.
The Huawei Connection
No definite proof has been found linking the Chinese state to these actions. Yet many are worried that the Chinese government may play a role in such attacks. A recent white paper from the University of Cambridge, entitled “The Snooping Dragon“, claims to have documented concrete evidence of state officials using malware to infiltrate pro-Tibet activist computers.
The link to China’s state communications company, Huawai, appears particularly suspect. Huawei technology is at the core of BT’s new 10 billion communications upgrade. A NetworkedWorld article discusses the close connections between Huawei and the Chinese military. It reports,
Huawei maintains deep ties with the Chinese military, which serves a multi-faceted role as an important customer, as well as Huawei’s political patron and research and development partner.
Both the government and the military tout Huawei as a national champion, and the company is currently China’s largest, fastest-growing, and most impressive telecommunications equipment manufacturer.
In a related report entitled “Spy Chiefs Fear Chinese Security Threat”, The Times Online reports,
INTELLIGENCE chiefs have warned that China may have gained the capability to shut down Britain by crippling its telecoms and utilities.
According to the sources, the ministerial committee on national security was told at the January meeting that Huawei components that form key parts of BT’s new network might already contain malicious elements waiting to be activated by China.
Working through Huawei, China was already equipped to make “covert modifications” or to “compromise equipment in ways that are very hard to detect” and that might later “remotely disrupt or even permanently disable the network”, the meeting was told.
This would be likely to have a “significant impact on critical services” such as power and water supplies, food distribution, the financial system and transport, which were dependent on computers to operate.
INTELLIGENCE chiefs have warned that China may have gained the capability to shut down Britain by crippling its telecoms and utilities.
According to the sources, the ministerial committee on national security was told at the January meeting that Huawei components that form key parts of BT’s new network might already contain malicious elements waiting to be activated by China.
Working through Huawei, China was already equipped to make “covert modifications” or to “compromise equipment in ways that are very hard to detect” and that might later “remotely disrupt or even permanently disable the network”, the meeting was told.
This would be likely to have a “significant impact on critical services” such as power and water supplies, food distribution, the financial system and transport, which were dependent on computers to operate.
Discussion
Many wonder how Huawei might accomplish these security breaches. WTWU at SpyBlog suggests that it would be silly for Huawei to do so. They write,
It would be incredibly risky for the Chinese Government to attempt to insert such trojan horse “backdoors” into Huawei manufactured equipment, especially into the hardware, where the evidence cannot be deleted after a Denial of Service attack etc.
The cost of using such a capability, if it even exists, would be to immediately destroy the multi billion pound Huawei company commercially.
Yet in a recent confidential interview, an ex-Huawei employee suggested that the speed of sales and the level of complexity of such systems has little to no quality control checking or safety assurance of the components.
It would therefore be close to impossible to monitor the security of the commercial services sold by Huawei, given the tremendous volume of such sales.
Worse than hardware might be a software backdoor, which is easily modifiable and less risky than hardware breaches.
Although there is no evidence that Huawei is related to the kinds of cyberattacks and web espionage efforts such as GhostNet, there does appear to be a plausible connection.
The impact of such a link, and its relationship to development and humanitarian aid, may be worthy of monitoring and consideration.




 Posted by hfpblog
Posted by hfpblog 


 Add our RSS feed
Add our RSS feed